Tor Browser 2024 utilizes the Tor network, which is a series of virtual tunnels, to allow people and groups to improve their privacy and security on the Internet. It also enables software developers to create new communication tools with built-in privacy features.
How does the Tor Browser keep my internet activity anonymous?
The Tor Browser uses the Tor network, which consists of more than six thousand relays located worldwide, to hide the users' location and online traffic. This ensures anonymity and avoids your activities from being seen by others.
What is Tor Browser?
The Tor Browser is the flagship product from the Tor Project. The web browser is based on a modified version of Mozilla Firefox ESR that includes extras like the Tor proxy, TorButton, TorLauncher, NoScript, and HTTPS Everywhere extensions.
Who uses the Tor Browser?
With Tor Browser having made Tor more accessible to everyday internet users and activists, Tor was an instrumental tool during the Arab Spring beginning in late 2010. It not only protected people's identity online but also allowed them to access critical resources, social media, and websites which were blocked.
Individuals use Tor to keep websites from tracking them and their family members, or to connect to news sites, instant messaging services, or the like when these are blocked by their local Internet providers. Tor's hidden services let users publish web sites and other services without needing to reveal the location of the site. Individuals also use Tor for socially sensitive communication: chat rooms and web forums for rape and abuse survivors, or people with illnesses.
Journalists use Tor to communicate more safely with whistleblowers and dissidents. Non-governmental organizations (NGOs) use Tor to allow their workers to connect to their home website while they're in a foreign country, without notifying everybody nearby that they're working with that organization.
Groups such as Indymedia recommend Tor for safeguarding their members' online privacy and security. Activist groups like the Electronic Frontier Foundation (EFF) recommend Tor as a mechanism for maintaining civil liberties online. Corporations use Tor as a safe way to conduct competitive analysis, and to protect sensitive procurement patterns from eavesdroppers. They also use it to replace traditional VPNs, which reveal the exact amount and timing of communication. Which locations have employees working late? Which locations have employees consulting job-hunting websites? Which research divisions are communicating with the company's patent lawyers?
A branch of the U.S. Navy uses Tor for open source intelligence gathering, and one of its teams used Tor while deployed in the Middle East recently. Law enforcement uses Tor for visiting or surveilling web sites without leaving government IP addresses in their web logs, and for security during sting operations.
Is Tor better than a VPN?
Tor is not a VPN. Tor is a free browser similar to Chrome or Firefox, but it includes features that encrypt your IP address, making your browsing sessions private. A VPN (Virtual Private Network) is software that can change your IP address when you use any browser installed on your PC. To learn more about VPNs, you can read this article.
What's New
All Platforms
- Bug tor-browser#42288: Allow language spoofing in status messages
Windows + macOS + Linux
- Bug tor-browser#42302: The allowed ports string contains a typo
- Bug tor-browser#42231: Improve the network monitor patch for http onion resources
- Bug tor-browser#42299: After adding incorrect bridge addres on user cannot go back to the Connection page
Linux
- Bug tor-browser#17560: Downloaded URLs disk leak on Linux
- Bug tor-browser#42306: Tor Browser crashes when extensions popups are opened with Wayland enabled
- Bug tor-browser-build#41017: Disable Nvidia shader cache
Build SystemAll Platforms
- Bug tor-browser-build#41027: Remove tb-build-04 and tb-build-05 from tools/signing/download-unsigned-sha256sums-gpg-signatures-from-people-tpo
- Bug tor-browser-build#40936: Revert tor-browser-build#40933
- Bug tor-browser-build#40995: Use cdn.stagemole.eu instead of cdn.devmole.eu in download-unsigned-sha256sums-gpg-signatures-from-people-tpo
- Bug rbm#40064: Using exec on project with no git_url/hg_url is causing warning
Windows + macOS + Linux
- Bug tor-browser-build#41031: Add command to unsign .mar files and compare with sha256sums-unsigned-build.txt
Windows
- Bug tor-browser-build#41030: Add command to unsign .exe files and compare with sha256sums-unsigned-build.txt
Android
- Bug tor-browser-build#41024: Fix android filenames in Release Prep issue templates
Release notes for Tor Browser 13.0.5
This release updates Firefox to 115.5.0esr, tor to 0.4.8.9 and OpenSSL to 3.0.12. In addition, it also includes some bug fixes (see changelog for details).
The full changelog since Tor Browser 13.0.3 is:
All Platforms
- Updated OpenSSL to 3.0.12
- Updated tor to 0.4.8.9
- Bug tor-browser#42275: Rebase Tor Browser Stable to 115.5.0esr
- Bug tor-browser#42277: Enable storage.sync to fix broken webextensions
Windows + macOS + Linux
- Updated Firefox to 115.5.0esr
- Bug tor-browser#41341: Fix style and position of "Always Prioritize Onions" wingpanel
- Bug tor-browser#42108: Tor Circuit button not shown if TLS handshake fails
- Bug tor-browser#42184: Setting "Homepage and new windows" ignores "Blank Page" value
- Bug tor-browser#42188: Donations are asked repeatedly when I click New identity button
- Bug tor-browser#42194: Blank Net Error page on name resolution failure
Windows + macOS
- Bug tor-browser#42154: Empty the clipboard on browser shutdown only if content comes from private browsing windows
Android
- Updated GeckoView to 115.5.0esr
- Bug tor-browser#42074: YEC 2023 Takeover for Android Stable
- Bug tor-browser#42287: Backport security fixes (Android & wontfix) from Firefox 120 to 115.5 - based Tor Browser
- Build SystemAll Platforms
- Update Go to 1.21.4
- Bug tor-browser-build#40934: Remove $bundle_locales from signing scripts now that we're on ALL for everything
- Bug tor-browser-build#40982: Fix logging in tools/signing/do-all-signing
- Bug tor-browser-build#40989: Add .nobackup files to reproducible and disposable directores
- Bug tor-browser-build#41006: Fix typo in finished-signing-clean-linux signer
macOS
- Bug tor-browser-build#29815: Sign our macOS bundles on Linux
- Bug tor-browser-build#41005: Unpack macOS bundle to /var/tmp instead of /tmp in rcodesign-notary-submit step
- Bug tor-browser-build#41007: gatekeeper-bundling.sh refers to old .tar.gz archive
- Bug tor-browser-build#41014: Update libdmg-hfsplus to drop the OpenSSL patch
- Bug tor-browser-build#41020: Opening MacOS dmg file is causing a warning, since 13.0
Previous Release Notes:
This release backports important security updates from Firefox 115.4.0esr and
This release updates Firefox to 115.4.0esr, including bug fixes, stability improvements and important security updates. We also backported the Android-specific security updates from Firefox 119.
All Platforms
- Bug tor-browser#42185: Rebase stable browsers on top of 115.4.0esr
- Bug tor-browser#42191: Backport security fixes (Android & wontfix) from Firefox 119 to 115.4 - based Tor Browser
- Bug tor-browser-build#40975: libstdc++.so.6 is included twice in tor-browser
Windows + macOS + Linux
- Updated Firefox to 115.4.0esr
- Bug tor-browser#42182: Default Search Engine Does Not Persist Through Shift to New Identity
Android
- Updated GeckoView to 115.4.0esr
Build SystemAll Platforms
- Updated Go to 1.21.3
- Bug tor-browser-build#40976: Update download-unsigned-sha256sums-gpg-signatures-from-people-tpo to fetch from tb-build-02 and tb-build-03
- Bug rbm#40062: Copy input directories to containers recursively
Windows + Linux
- Bug tor-browser-build#40991: Fix creation of downloads-windows-x86_64.json and downloads-linux-x86_64.json
Windows
- Bug tor-browser-build#40984: The PDBs for .exe are not included
Linux
- Bug tor-browser-build#40979: Add redirects from old Linux bundle filename to the new one
Previous Release Notes:
This is our first stable release based on Firefox ESR 115, incorporating a year's worth of changes shipped upstream. As part of this process we've also completed our annual ESR transition audit, where we review Firefox's changelog for issues that may negatively affect the privacy and security of Tor Browser users and disable any problematic patches where necessary. Our final reports from this audit are now available in the tor-browser-spec repository on our Gitlab instance.
Particularly notable are the accessibility improvements we've gained as a result of the transition to Firefox ESR 115. While eagle-eyed users may notice small visual changes to the user interface (for example, internal links are now underlined), Tor Browser 13.0 is our first release to inherit the redesigned accessibility engine introduced by Mozilla in Firefox 113. This change promises to improve performance significantly for people who use screen readers and other assistive technology.
Refreshed application icons
Earlier this year we spent some time artworking the Mullvad Browser logo into the various assets needed to support its release – including application, installer and document icons that conform to each platform's conventions. While getting up to speed with the current requirements for each platform, we identified a number of gaps with Tor Browser too, and started working on new icons for Tor Browser in parallel.
For context, Tor Browser's current icon (sometimes referred to as the "onion logo") was selected by community poll over four years ago to succeed the older purple and green globe in Tor Browser 8.5. Given the community's involvement in its selection, its recognizability by netizens, and the simple fact that we still love the existing icon, we chose to focus on refining rather than replacing it entirely.
One of the motivations behind work like this is our philosophy that privacy-preserving products shouldn't be purely utilitarian, but can also spark joy. However there are practical benefits too: adhering to platform conventions provides better consistency, discernible application and installer icons help prevent user error, and attracting new users benefits everyone because anonymity loves company.
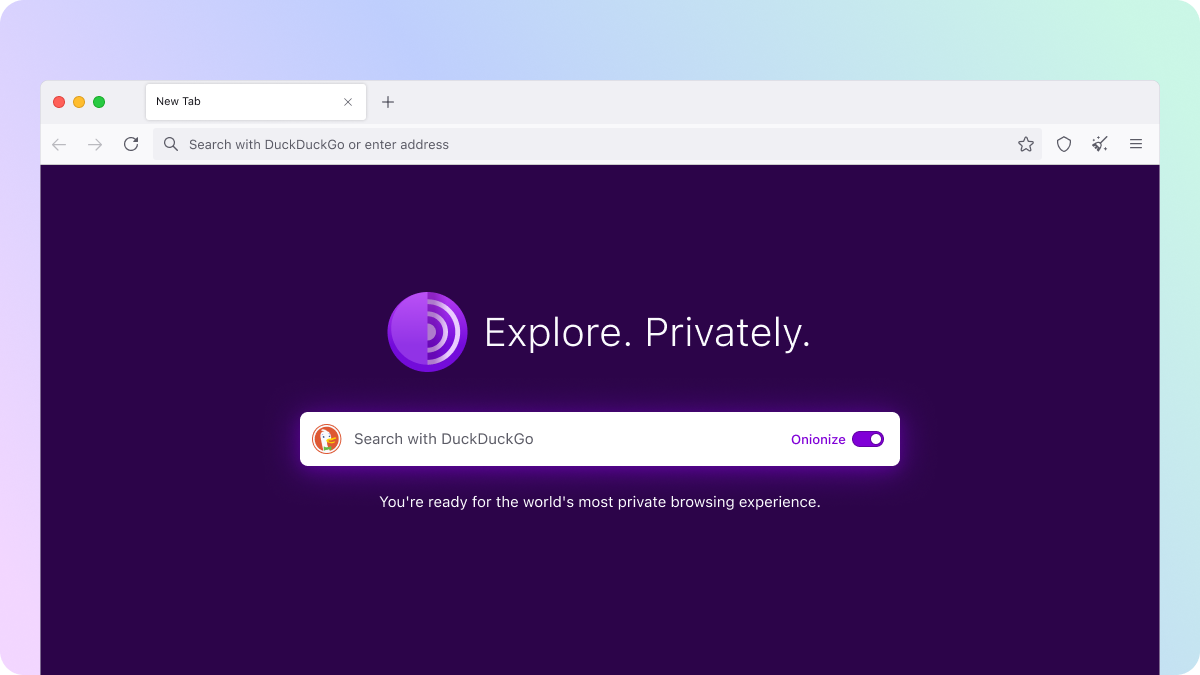
New homepage
For the past year we've been working on a significant rewrite of Tor Browser's back-end, which recently provided us with the opportunity to rebuild one of the few internal pages that hasn't changed in a while: the homepage (often referred to by its internal reference, "about:tor"). Tor Browser 13.0's homepage now features the new application icons, a simplified design, and the ability to "onionize" your DuckDuckGo searches by switching to the DuckDuckGo onion site. Continuing the work that began in Tor Browser 12.5 to improve the browser's accessibility, the redesigned homepage also offers better support for users of screen readers and other assistive technology too.
Existing Tor Browser users can rejoice that the "red screen of death" – an infamous error state that the previous homepage would occasionally trip itself into – is long gone. As part of the back-end rewrite we've removed the automatic Tor network connectivity check that was a hold-over from the legacy tor-launcher, where bootstrapping was handled by an extension that ran before the browser interface appeared. As a result of the tighter tor integration and in-browser bootstrapping experience introduced in Tor Browser 10.5, the old logic behind this check would often fail and present some users with the red screen of death, even if their connection was fine.
In fact, all of the reports we've received of users hitting this screen with the default tor configuration since Tor Browser 10.5 have proven to be false positives, causing undue alarm. Although the check is arguably still useful for users running non-default configurations, neither of the main environments which do so – Tails and Whonix – use about:tor as their default new-tab or home pages. For everyone else, we've added a new banner to the redesigned homepage in place of the red screen of death to check that tor is connected and working as expected.
Bigger new windows
The explanation for how and why Tor Browser works this way is going to get into the weeds a little, so be warned. However the main thing to take away is that new windows should be bigger by default and present themselves in a more useful landscape aspect-ratio for the majority of desktop users in Tor Browser 13.0. Now, about those weeds...
Letterboxing was introduced in Tor Browser 9.0 to allow users to resize their browser window without fear of being fingerprinted by rounding the inner content window (sometimes referred to as the "viewport") down to multiples of 200 x 100 pixels. This technique works by grouping the window sizes of most users into a series of common "buckets", protecting individual users within those buckets from being singled-out based on their window or screen size.
In order to preserve these protections when opening new windows, Tor Browser overrides platform defaults and will instead select a size that conforms to our letterboxing steps up to a maximum of 1000 x 1000 pixels. However, while that may have been fine in the past, a max width of 1000px is no longer suitable for the modern web. For example, on many newer websites the first responsive break point lies somewhere in the range of 1000 – 1200px, meaning by default Tor Browser users would receive website menus and layouts intended for tablet and mobile devices. Alternatively, on certain websites, users would receive the desktop version but with the annoyance of a horizontal scroll bar instead. This, naturally, would lead to users of these websites needing to expand each new window manually before it's usable.
In response we've bumped up the max size of new windows up to 1400 x 900 pixels and amended the letterboxing steps to match. Thanks to the increase in width, Tor Browser for desktop should no longer trigger responsive break points on larger screens and the vast majority of our desktop users will see a familiar landscape aspect-ratio more in-keeping with modern browsers. This particular size was chosen by crunching the numbers to offer greater real estate for new windows without increasing the number of buckets past the point of their usefulness. As an added bonus, we also expect that Tor Browser users will not feel the need to manually change their window size as frequently as before – thereby keeping more users aligned to the default buckets.
All Platforms
- Updated tor to 0.4.8.7
- Updated OpenSSL to 3.0.11
- Bug tor-browser-spec#40050: FF103 Audit
- Bug tor-browser-spec#40051: FF104 Audit
- Bug tor-browser-spec#40052: FF105 Audit
- Bug tor-browser-spec#40053: FF106 Audit
- Bug tor-browser-spec#40054: FF107 Audit
- Bug tor-browser-spec#40055: FF108 Audit
- Bug tor-browser-spec#40056: FF109 Audit
- Bug tor-browser-spec#40057: FF110 Audit
- Bug tor-browser-spec#40058: FF111 Audit
- Bug tor-browser-spec#40059: FF112 Audit
- Bug tor-browser-spec#40060: FF113 Audit
- Bug tor-browser-spec#40061: FF114 Audit
- Bug tor-browser-spec#40062: FF115 Audit
- Bug tor-browser#26277: When "Safest" setting is enabled searching using duckduckgo should always use the Non-Javascript site for searches
- Bug tor-browser#40577: Add "suggest url" in DDG onion's manifest
- Bug tor-browser#40938: Migrate remaining torbutton functionality to tor-browser
- Bug tor-browser#41092: Enable tracking query parameters stripping
- Bug tor-browser#41327: Disable UrlbarProviderInterventions
- Bug tor-browser#41399: Update Mozilla's patch for Bug 1675054 to enable brotli encoding for HTTP onions as well
- Bug tor-browser#41477: Review some extensions.* preferences
- Bug tor-browser#41496: Review 000-tor-browser.js and 001-base-profile.js for 115
- Bug tor-browser#41576: ESR115: ensure no remote calls for weather & addon suggestions
- Bug tor-browser#41605: Remove unused assets from torbutton (preferences-mobile.css)
- Bug tor-browser#41675: Remove javascript.options.large_arraybuffers
- Bug tor-browser#41727: WebRTC privacy-hardening settings
- Bug tor-browser#41740: ESR115: change devicePixelRatio spoof to 2 in alpha for testing
- Bug tor-browser#41752: Review changes done by Bug 41565
- Bug tor-browser#41796: Rebase Tor Browser to Firefox 115
- Bug tor-browser#41797: Lock RFP in release builds
- Bug tor-browser#41934: Websocket raises DOMException on http onions in 13.0a1
- Bug tor-browser#41936: Review Mozilla 1770158: Use double-conversion library instead of dtoa for string-to-double conversion
- Bug tor-browser#41937: Review Mozilla 1780014: Add specific telemetry for conservative and first-try handshakes
- Bug tor-browser#41938: Review Mozilla 1769994: On systems with IPv6 preferred DNS resolution clients will fail to connect when "localhost" is used as host for the WebSocket server
- Bug tor-browser#41939: Review Mozilla 1728871: Support fetching data from Remote Setting
- Bug tor-browser#41941: Review Mozilla 1775254: Improve Math.pow accuracy for large exponents
- Bug tor-browser#41943: Lock javascript.options.spectre.disable_for_isolated_content to false
- Bug tor-browser#41945: Review Mozilla 1783019: Add a cookie banner service to automatically handle website cookie banners
- Bug tor-browser#41946: Review Mozilla 1782579: Add a locale parameter to the text recognition API
- Bug tor-browser#41947: Review Mozilla 1779005: Broken since Firefox 102.0: no instant fallback to direct connection when proxy became unreachable while runtime
- Bug tor-browser#41950: Review Mozilla 1788668: Add the possibility to check that the clipboard contains some pdfjs stuff
- Bug tor-browser#41951: Review Mozilla 1790681: Enable separatePrivateDefault by default
- Bug tor-browser#41959: Review Mozilla 1795944: Remove descriptionheightworkaround
- Bug tor-browser#41960: Review Mozilla 1797896: Proxy environment variables should be upper case / case insensitive
- Bug tor-browser#41961: Review Mozilla 1798868: Hide cookie banner handling UI by default
- Bug tor-browser#41969: Review Mozilla 1746983: Re-enable pingsender2
- Bug tor-browser#41970: Review Mozilla 17909270: WebRTC bypasses Network settings & proxy.onRequest
- Bug tor-browser#41984: Rename languageNotification.ftl to base-browser.ftl
- Bug tor-browser#42013: Review Mozilla 1834374: Do not call EmptyClipboard() in nsBaseClipboard destructor
- Bug tor-browser#42014: Review Mozilla 1832791: Implement a Remote Settings for the Quarantined Domains pref
- Bug tor-browser#42015: Review Mozilla 1830890: Keep a history window of WebRTC stats for about:webrtc
- Bug tor-browser#42019: Empty browser's clipboard on browser shutdown
- Bug tor-browser#42026: Disable cookie banner service and UI.
- Bug tor-browser#42029: Defense-in-depth: disable non-proxied UDP WebRTC
- Bug tor-browser#42034: aboutTBUpdate.dtd is duplicated
- Bug tor-browser#42043: Disable gUM: media.devices.enumerate.legacy.enabled
- Bug tor-browser#42061: Move the alpha update channel creation to a commit on its own
- Bug tor-browser#42084: Race condition with language preferences may make spoof_english ineffective
- Bug tor-browser#42085: NEWNYM signal missing on Whonix
- Bug tor-browser#42094: Disable media.aboutwebrtc.hist.enabled as security in-depth
- Bug tor-browser#42120: Use foursquare as domain front for snowflake
- Bug tor-browser-build#40887: Update Webtunnel version to 38eb5505
Windows + macOS + Linux
- Updated Firefox to 115.3.1esr
- Bug tor-browser#30556: Re-evaluate letterboxing dimension choices
- Bug tor-browser#32328: Improve error recovery from the red screen of death
- Bug tor-browser#33282: Increase the max width of new windows
- Bug tor-browser#33955: Selecting "Copy image" from menu leaks the source URL to the clipboard. This data is often dereferenced by other applications.
- Bug tor-browser#40175: Connections in reader mode are not FPI
- Bug tor-browser#40982: Cleanup maps in tor-circuit-display
- Bug tor-browser#40983: Move not UI-related torbutton.js code to modules
- Bug tor-browser#41165: Crash with debug assertions enabled
- Bug tor-browser#41333: Modernize Tor Browser's new-tab page (about:tor)
- Bug tor-browser#41423: about:tor semantic and accessibility problems
- Bug tor-browser#41528: Hard-coded English "based on Mozilla Firefox" appears in version in "About" dialog
- Bug tor-browser#41581: ESR115: figure out extension pinning / unified Extensions
- Bug tor-browser#41639: Fix the wordmark (title and background) of the "About Tor Browser" window
- Bug tor-browser#41642: Do not hide new PBM in the hamburger menu if auto PBM is not enabled
- Bug tor-browser#41651: Use moz-toggle in connection preferences
- Bug tor-browser#41691: "Firefox Suggest" text appearing in UI
- Bug tor-browser#41717: Bookmark toolbar visibility on new tabs is not honored when new tab page is not about:blank
- Bug tor-browser#41739: Remove "Website appearance"
- Bug tor-browser#41741: Refactor the domain isolator and new circuit
- Bug tor-browser#41765: TTP-02-006 WP1: Information leaks via custom homepage (Low)
- Bug tor-browser#41766: TTP-02-001 WP1: XSS in TorConnect's captive portal (Info)
- Bug tor-browser#41771: Decide what to do for firefoxview
- Bug tor-browser#41774: Hide the new "Switching to a new device" help menu item
- Bug tor-browser#41791: Copying page contents also puts the source URL on the clipboard
- Bug tor-browser#41812: Review layout for XUL elements
- Bug tor-browser#41813: Look out for links missing underlines in ESR 115-based alphas
- Bug tor-browser#41821: Fix the proxy type in the proxy modal of about:preferences in 13.0
- Bug tor-browser#41822: The default browser button came back on 115
- Bug tor-browser#41833: Reload extensions on new identity
- Bug tor-browser#41834: Hide "Can't Be Removed - learn more" menu line for uninstallable add-ons
- Bug tor-browser#41842: Remove the old removal logics from Torbutton
- Bug tor-browser#41844: Stop using the control port directly
- Bug tor-browser#41845: Stop forcing (bad) pref values for non-PBM users
- Bug tor-browser#41852: Review the Tor Check Service UX
- Bug tor-browser#41864: TOR_CONTROL_HOST and TOR_SOCKS_HOST do not work as expected when the browser launches tor
- Bug tor-browser#41865: Use --text-color-deemphasized rather than --panel-description-color
- Bug tor-browser#41874: Visual & A11 regressions in add-on badges
- Bug tor-browser#41876: Remove Firefox View from title bar
- Bug tor-browser#41877: NoScript seems to be blocking by default in the first 115-based testbuild
- Bug tor-browser#41881: Developer tools/Network/New Request remembers requests
- Bug tor-browser#41886: Downloads drop-down panel has new-line/line-break between every word in the 'Be careful opening downloads' warning
- Bug tor-browser#41904: The log textarea doesn't resize anymore
- Bug tor-browser#41906: Hide about:preferences#privacy > DNS over HTTPS section
- Bug tor-browser#41907: The bootstrap is interrupted without any errors if the process becomes ready when already bootstrapping
- Bug tor-browser#41912: "Use Current Bridges" is shown for users even when there aren't any current bridges
- Bug tor-browser#41922: Unify the bridge line parsers
- Bug tor-browser#41923: The path normalization results in warnings
- Bug tor-browser#41924: Small refactors for TorProcess
- Bug tor-browser#41925: Remove the torbutton startup observer
- Bug tor-browser#41926: Refactor the control port client implementation
- Bug tor-browser#41931: Regression: new window leaks outer window
- Bug tor-browser#41935: Improve new window & letterboxing dimensions
- Bug tor-browser#41940: Review Mozilla 1739348: When a filetype is set to "always ask" and the user makes a save/open choice in the dialog, we should not also open the downloads panel
- Bug tor-browser#41949: Review Mozilla 1782578: Implement a context menu modal for text recognition
- Bug tor-browser#41954: Inputs in the request a bridge dialog are cut-off in 13.0 alpha
- Bug tor-browser#41957: Revert to Fx's default identity block style for internal pages
- Bug tor-browser#41958: Console error when closing tor browser with about:preferences open
- Bug tor-browser#41964: emojiAnnotations not defined in time in connection preferences
- Bug tor-browser#41965: TorConnect error when opening browser tools
- Bug tor-browser#41971: Update Tails URL in downloads warning
- Bug tor-browser#41973: Custom wingpanels don't line up with their toolbar icons in 13.0 alpha
- Bug tor-browser#41974: De-emphasized text in custom components is no longer gray in 13.0 alpha
- Bug tor-browser#41975: Downloads warning text too narrow in 13.0 alpha
- Bug tor-browser#41976: Bottom padding on collapsed bridge cards has increased in 13.0 alpha
- Bug tor-browser#41977: Hide the "Learn more" link in bridge cards
- Bug tor-browser#41980: Circuit display headline is misaligned in 13.0 alpha
- Bug tor-browser#41981: Review Mozilla 1800675: Add about:preferences entry for cookie banner handling
- Bug tor-browser#41983: Review Mozilla 1770447: Create a reusable "support-link" widget
- Bug tor-browser#41986: Fix the control port password handling
- Bug tor-browser#41994: CSS (and other assets) of some websites blocked in 13.0 alpha
- Bug tor-browser#42022: Prevent extension search engines from breaking the whole search system
- Bug tor-browser#42027: Create a Base Browser version of migrateUI
- Bug tor-browser#42037: Disable about:firefoxview
- Bug tor-browser#42041: TBB --allow-remote mixes up with plain Firefox
- Bug tor-browser#42045: Circuit panel overflows with long ipv6 addresses
- Bug tor-browser#42046: Remove XUL layout hacks from base browser
- Bug tor-browser#42047: Remove layout hacks from tor browser preferences
- Bug tor-browser#42050: Bring back Save As... dialog as default
- Bug tor-browser#42073: Add simplified onion pattern to the new homepage
- Bug tor-browser#42075: Fix link spacing and underline on new homepage
- Bug tor-browser#42079: TorConnect: handle switching from Bootstrapped to Configuring state
- Bug tor-browser#42083: RemoteSecuritySettings.init throws error in console
- Bug tor-browser#42091: Onion authorization prompt overflows
- Bug tor-browser#42092: Onion services key table display problems.
- Bug tor-browser#42098: Implement Windows installer icons
- Bug tor-browser#42100: Connect Assist dropdown text not centered
- Bug tor-browser#42102: TorProcess says the SOCKS port is not valid even though it is
- Bug tor-browser#42109: Onion services keys table has empty column headers.
- Bug tor-browser#42110: Add a utility module for shared UI methods needed for several tor browser components
- Bug tor-browser#42126: moat and connect assist broken for people who can't reach domain front
- Bug tor-browser#42129: Disable the Tor restart prompt if shouldStartAndOwnTor is false
- Bug tor-browser#42131: Tor Browser 13.0a5 does not track circuits created before Tor Browser started
- Bug tor-browser#42132: The new control port handling in Tor Browser 13 breaks a Tails security feature
- Bug tor-browser#42138: Disable apz.overscroll.enabled pref
- Bug tor-browser#42155: Drop the unused code for the old bridge removal warning
- Bug tor-browser#42159: Responsive Design Mode not working correctly
- Bug tor-browser#42160: Allow specifying a TOR_PROVIDER=none to configure only the proxy settings during the TorProviderBuilder initialization
- Bug tor-browser#42166: New identity dialog missing accessible name
- Bug tor-browser#42167: Make the preference auto-focus more reliable
- Bug tor-browser-build#40821: The update details URL is wrong in alphas
- Bug tor-browser-build#40893: Update (Noto) fonts for 13.0
- Bug tor-browser-build#40924: Customize MOZ_APP_REMOTINGNAME instead of passing --name and --class
- Bug tor-browser-build#40938: Copy the new tor-browser.ftl file to the appropriate directory
Windows + Android
- Bug tor-browser-build#40930: Upate zlib to 1.3 after 13.0a3
Windows
- Bug tor-browser#40737: Revert backout of Mozilla's fix for bug 1724777
- Bug tor-browser#41658: Create new installer icons for Windows
- Bug tor-browser#41798: Stop building private_browsing.exe on Windows
- Bug tor-browser#41806: Prevent Private Browsing start menu item to be added automatically
- Bug tor-browser#41942: Review Mozilla 1682520: Use the WER runtime exception module to catch early crashes
- Bug tor-browser#41944: Review Mozilla 1774083: Add Surrogate COM Server to handle native Windows notifications when Firefox is closed.
- Bug tor-browser#42008: Review Mozilla 1808146: Copying images from Pixiv and pasting them in certain programs is broken
- Bug tor-browser#42010: Review Mozilla 1810641: Enable overscroll on Windows on all channels
- Bug tor-browser#42087: Implement Windows application icons
- Bug tor-browser-build#40954: Implement Windows installer icons
macOS
- Bug tor-browser#41948: Review Mozilla 1782981: Hide the text recognition context menu if the macOS version doesn't support APIs
- Bug tor-browser#41955: Update macOS volume window background
- Bug tor-browser#41982: Review Mozilla 1762392: Add Cocoa platform support for paste files
- Bug tor-browser#42057: Disable Platform text-recognition functionality
- Bug tor-browser#42078: Implement MacOS application icons
- Bug tor-browser#42147: Add browser.helperApps.deleteTempFileOnExit to our profile
Linux
- Bug tor-browser#41509: After update, KDE Plasma identifies Tor Browser Nightly window group as "firefox-nightly"
- Bug tor-browser#41884: Linux: set browser.tabs.searchclipboardfor.middleclick to false
- Bug tor-browser#42088: Implement Linux application icons
- Bug tor-browser-build#40576: Fontconfig warning: remove 'blank' configuration
Android
- Updated GeckoView to 115.3.1esr
- Bug tor-browser#41878: firefox-mobile: refactor tor bootstrap off deleted onboarding path
- Bug tor-browser#41882: Update DuckDuckGo icons
- Bug tor-browser#41911: Firefox-Android tor bootstrap connect button css broken
- Bug tor-browser#41928: Backport Android-specific security fixes from Firefox 116 to ESR 102.14 / 115.1 - based Tor Browser
- Bug tor-browser#41972: Disable Firefox onboarding in 13.0
- Bug tor-browser#41990: Review Mozilla 1811531: Add 'site' query parameter to Pocket sponsored stories request
- Bug tor-browser#41991: Review Mozilla 1812518: Allow a custom View for 3rd party downloads
- Bug tor-browser#41993: Review Mozilla 1810761: Add API for saving a PDF
- Bug tor-browser#41996: App includes com.google.android.gms.permission.AD_ID permission
- Bug tor-browser#41997: com.adjust.sdk.Adjust library enables AD_ID permission even though we aren't using it
- Bug tor-browser#41999: TB13.0a2 android: center text on connect button
- Bug tor-browser#42001: Hide 'Open links in external app' settings option and force defaults
- Bug tor-browser#42002: Review Mozilla 1809305: Allow user to copy an image to the clipboard
- Bug tor-browser#42003: Review Mozilla 1819431: Reimplement default browser notification with Nimbus Messaging equivalent
- Bug tor-browser#42004: Review Mozilla 1818015: Use a custom tab or the view we use for Sync onboarding for the Privacy button
- Bug tor-browser#42005: Review Mozilla 1816932: Add Maps to app links common sub domains
- Bug tor-browser#42006: Review Mozilla 1817726: Allow sharing current tab URL from Android's Recents (App Overview) screen.
- Bug tor-browser#42007: Review Mozilla 1805450: Allow users to submit site support requests in Fenix
- Bug tor-browser#42012: Review Mozilla 1810629: add an Android shortcut to go straight to the login and passwords page
- Bug tor-browser#42016: Review Mozilla 1832069: Implement Google Play Referrer Library to fetch referrer URL
- Bug tor-browser#42018: Rebase Firefox for Android to 115.2.1
- Bug tor-browser#42023: Remove FF what's new from Android
- Bug tor-browser#42038: TBA Alpha - inscriptions Tor Browser Alpha and FireFox Browser simultaneously on the start screen
- Bug tor-browser#42074: YEC 2023 Takeover for Android Stable
- Bug tor-browser#42076: Theme is visible in options, but shouldn't be
- Bug tor-browser#42089: Disable the Cookie Banner Reduction site support requests (Mozilla 1805450)
- Bug tor-browser#42114: Disable Allow sharing current tab URL from Android's Recents screen in private browsing mode
- Bug tor-browser#42115: Enhanced Tracking Protection can still be enabled
- Bug tor-browser#42122: playstore console crashes: java.lang.NoSuchMethodError
- Bug tor-browser#42133: Remove "Total Cookie Protection" popup
- Bug tor-browser#42134: Remove Android icon shortcuts
- Bug tor-browser#42156: Screenshot allowing still blocks homescreen (android)
- Bug tor-browser#42157: Fix Help button URL
- Bug tor-browser#42165: Remove "Add to shortcuts" and "Remove from shortcuts" buttons
- Bug tor-browser#42158: Remove "Customize Homepage" button
- Bug tor-browser-build#40740: Tor Browser for Android's snowflake ClientTransportPlugin seems to be out of date
- Bug tor-browser-build#40919: Fix nimbus-fml reproducibility of 13.0a2-build1
- Bug tor-browser-build#40941: Remove PT process options on Android